Document #: HHS-OCIO-OES-2020-12-011
Version #: 2.0
Last Reviewed: 12/2020
Next Review: 12/2023
Owner: OCIO/OES
Approved By: Perryn B. Ashmore, Chief Information Officer (CIO) (Acting)
Table of Contents
- Nature of Changes
- Purpose
- Background
- Scope
- Authorities
- Policy
- Roles and Responsibilities
- 7.1. HHS Chief Information Officer (CIO)
- 7.2. HHS Chief Enterprise Architect (CEA)
- 7.3. HHS Chief Information Security Officer (CISO)
- 7.4. HHS Senior Agency Official for Privacy (SAOP)
- 7.5. HHS IT Capital Planning and Investment Control (CPIC) Officer
- 7.6. Enterprise Architecture Review Board (EARB)
- 7.7. Vendor Management Office (VMO)
- 7.8. OpDiv CIO
- 7.9. OpDiv CEA
- 7.10. OpDiv CISO
- 7.11. OpDiv Senior Official for Privacy (SOP)
- 7.12. OpDiv IT CPIC Officer
- 7.13. Business Owner
- 7.14. System Owner
- Information and Assistance
- Effective Date and Implementation
- Approval
- Concurrence
Appendix D: Forms and Templates
1. Nature of Changes
The HHS Policy for IT System Inventory Management (hereafter Policy) supersedes the HHS-OCIO Policy for Management of the Enterprise IT System Inventory, July 2009 (HHS-OCIO-2009-0004).
Major revisions to this Policy include an updated list of authorities, new roles and responsibilities, and updated procedures, standards, and guidance. This Policy incorporates the most recent polices and directives as specified by Office of Management and Budget (OMB), National Institute of Standards and Technology (NIST), and Health and Human Services (herein HHS or Department).
NOTE: Appendices are subject to change at any time. The official version of this Policy resides in the Enterprise IT Policy Library.
2. Purpose
The purpose of this Policy is to direct HHS entities (i.e., Operating Divisions [OpDiv] and Staff Divisions [StaffDiv]) to establish and maintain an enterprise-wide inventory of HHS IT systems by providing guidance and baseline standards for maintaining a comprehensive inventory of all IT systems and related information. This Policy also establishes the authoritative source for the HHS IT System Inventory (henceforth “the IT System Inventory”) and the stewards responsible for maintaining the availability and accuracy of the information.
3. Background
The Office of Management and Budget (OMB) Circular A-130, Management of Federal Information Resources, directs that all federal agencies must, “maintain an inventory of the agency’s major information systems, information holdings, and dissemination products, at the level of detail that OMB and the agency determine is most appropriate for overseeing and managing the information resources….” Responsibility for the maintenance of the IT System Inventory is under the purview of the HHS Enterprise Architecture Program. Enterprise architecture is the discipline of proactively and holistically leading enterprise responses to disruptive forces by identifying and analyzing the execution of change toward desired business vision and outcomes. It encompasses a strategic information asset base, which defines the mission, the information necessary to perform the mission, the technologies necessary to perform the mission, and the transitional processes for implementing new technologies in response to changing mission needs.
Maintaining the IT System Inventory involves coordination and collaboration of various business and IT functional areas. It is essential that all HHS entities keep an accurate and current inventory of IT systems. Having visibility into the IT System Inventory across the Department will facilitate managing information resources, IT planning, budgeting, and acquisitions. A comprehensive IT System Inventory enables organizations to extract subsets of data based on their reporting and management requirements.
In the context of this Policy, an IT system is a discrete set of information resources organized for the collection, processing, maintenance, transmission, and dissemination of information, in accordance with defined procedures, owned or operated on behalf of, and automated to support HHS’s or an OpDiv’s mission. An IT system is the codification of business requirements, automated to support a specific mission- or business-related function. An IT system typically encompasses the hardware, software, information, data, applications, communications, and the human resources needed to run the IT system. An IT system is not a Cybersecurity system authorization boundary or a program.
IT Systems are a part of the overall HHS OCIO’s Office of Information Security’s (OIS) System Inventory which encompasses all authorization boundaries and their components, including their common control providers, programs, and information systems. In the context of Cybersecurity, an information system component is the same as an IT system. All HHS OIS System Inventory considerations should be understood as separate from, but complementary to, the requirements outlined in this Policy. For more information on the Cybersecurity requirements, please reference the HHS Standard for System Inventory Management.
All software inventory considerations should be understood as a separate initiative from the inventory requirements outlined in this Policy. For the purposes of this Policy, software is not just an element of the IT System Inventory, but also a separate inventory requirement. For more information regarding software inventory requirements, please reference the HHS Policy for IT Asset Management (ITAM).
OMB Circular A-11, Preparation, Submission, and Execution of the Budget, directs agencies to “have a disciplined capital programming process that addresses project prioritization between new assets and maintenance of existing assets, risk management and cost estimating to improve the accuracy of cost, schedule, and performance provided to management, and the other difficult challenges proposed by asset management and acquisition.” Capital Planning and Investment Control (CPIC) considerations are reflected throughout this Policy; however, specific requirements should be referenced from the HHS Policy for Capital Planning and Investment Control (CPIC) and the HHS Capital Planning Guide.
4. Scope
This Policy applies to all HHS entities and organizations that use or maintain IT systems that conduct business for, or are owned or operated on behalf of, the Department. This Policy does not supersede any applicable law or Department policy or guidance, unless specified in this document.
OpDivs/StaffDivs may create a more prescriptive policy specific to their requirements based on, but not less restrictive than, this Policy.
5. Authorities
The authorities for this Policy include:
Federal Law
- Clinger-Cohen Act (CCA) of 1996
- E-Government Act of 2002
- Federal Information Security Modernization Act (FISMA) of 2014
- Federal Information Technology Acquisition Reform Act (FITARA) of 2014
- FITARA Enhancement Act of 2017
- Making Electronic Government Accountable by Yielding Tangible Efficiencies (MEGABYTE) Act of 2016
OMB Circulars
- OMB Circular A-11, Preparation, Submission and Execution of the Budget
- OMB Circular A-130, Managing Information as a Strategic Resource
OMB Memoranda
- OMB Memorandum M-15-14, Management and Oversight of Federal Information Technology
- OMB Memorandum M-19-03, Strengthening the Cybersecurity of Federal Agencies by enhancing the High Value Asset Program
HHS Policy
- HHS Policy for Capital Planning and Investment Control (CPIC)
- HHS Policy for High Value Assets (HVA)
- HHS Policy for Information Technology Asset Management (ITAM)
- HHS Policy for Records Management
- HHS Information Security and Privacy Policy (IS2P)
Additional references may be found in Appendix E: References.
6. Policy
The overarching requirements and principles for this Policy are detailed in their respective sections below.
6.1. IT System Inventory Requirements
- All HHS entities must identify, register, and maintain a current and accurate inventory of IT systems that are updated as changes occur, or at a minimum, semiannually, throughout the lifecycle as defined in Appendix A. In accordance with federal mandates and regulations and HHS guidance, inventory data must comply with the minimum data standards detailed in Appendix B.1
- All HHS entities must decommission retired IT systems as detailed in Appendix A and in accordance with federal mandates, guidance, and regulations.
6.2. IT System Inventory Principles
- The IT System Inventory must include all IT systems that are owned by, or operated on behalf of, any HHS entity.
- The IT System Inventory and its related data must reside within the official HHS Enterprise Architecture Repository, as detailed at Appendix A.
- The IT System Inventory must adhere to federal laws and regulations, and HHS policies, standards, and guidance, as applicable, in Section 5 and Appendix A.
- The IT System Inventory must comply with the HHS Information Systems Security and Privacy Policy (IS2P) and the requirements as outlined in the HHS System Inventory Management Standard when working with the HHS OIS System Inventory records.
- The IT System Inventory must comply with the HHS Policy for IT Asset Management (ITAM) when developing a software specific inventory.
- The IT System Inventory must comply with the HHS Policy for Information Technology (IT) Capital Planning and Investment Control (CPIC) when developing an investment portfolio.
- The IT System Inventory must comply with requirements outlined in the HHS Policy for Records Management.
7. Roles and Responsibilities
7.1. HHS Chief Information Officer (CIO)
The HHS CIO, or designee, must:
- Ensure all IT systems and related information are maintained in HHS repositories, as detailed in Appendix A;
- Ensure that all HHS IT systems adhere to federal mandates and regulations, as well as HHS OIS and HHS Privacy and Information Management (PIM) policies and standards, as applicable to the IT System Inventory;
- Establish, implement, and maintain a current and accurate IT System Inventory that is managed through a change control process, as detailed in Appendix A;
- Provide a suite of enterprise-level tools to support an effective process of registering, maintaining, and sharing an inventory of IT systems;
- Ensure HHS entities adopt and implement this policy and its associated federal mandates, processes, and guidance, highlighted in Section 5 and in Appendix A;
- Ensure inventory compliance with the HHS Policy for Records Management; and
- Use IT System Inventory information to comply with various reporting and oversight requirements.
7.2. HHS Chief Enterprise Architect (CEA)
The HHS Chief Enterprise Architect, or designee, must:
- Serve as owner and manager of the IT System Inventory, a subset of the Chief Information Security Officer’s (CISO) HHS OIS Systems Inventory;
- Manage the life cycle of IT systems in the inventory, in coordination with HHS entities;
- Ensure IT System Inventory data gathering uses current and applicable technologies, methodologies, in accordance with relevant regulations, as detailed in Appendix A;
- Collaborate with the CISO in sharing applicable inventory information for analytics and to comply with various reporting requirements;
- Coordinate with the HHS SAOP in sharing applicable inventory information for analytics and to comply with various reporting requirements;
- Coordinate with the HHS CPIC Officer in sharing applicable inventory information for analytics and to comply with various reporting requirements;
- Collaborate with the Vendor Management Office (VMO) in the discovery and sharing of applicable HHS SAM inventory information to comply with various reporting requirements; and
- Ensure inventory compliance with the HHS Policy for Records Management.
7.3. HHS Chief Information Security Officer (CISO)
The HHS CISO, or designee, must:
- Collaborate with the CEA in the synchronization and sharing of HHS OIS System Inventory and IT System Inventory related information for analytics and to comply with various reporting requirements as detailed in Appendix A.
7.4. HHS Senior Agency Official for Privacy (SAOP)
The HHS SAOP, or designee, must:
- Collaborate with the CEA in the synchronization and sharing Cybersecurity, Privacy, and IT System Inventory related information for analytics and to comply with various reporting requirements as detailed in Appendix A.
7.5. HHS IT Capital Planning and Investment Control (CPIC) Officer
The HHS IT CPIC Officer must:
- Collaborate with the CEA in the synchronization and sharing IT Investment and IT System Inventory information for analytics and to comply with various reporting requirements as detailed in Appendix A.
7.6. Enterprise Architecture Review Board (EARB)
The EARB, must:
- Serve as an expert decision-making body to provide IT System Inventory standards, configuration management, and oversight; and
- Provide coordination and validation of the IT System Inventory data.
7.7. Vendor Management Office (VMO)
The VMO must:
- Collaborate with the CEA and CISO in the discovery and sharing of the HHS ITAM Inventory information for analytics and to comply with various reporting requirements as detailed in Appendix A.
7.8. OpDiv CIO
Each OpDiv’s CIO, or designee, must:
- Ensure OpDiv IT System Inventory information is in compliance with this Policy;
- Ensure that the OpDiv’s HHS OIS System Inventory and the IT System Inventory are maintained in the appropriate HHS Enterprise repositories; and
- Ensure that the OpDiv’s HHS OIS System Inventory and the IT System Inventory adhere to federal mandates and regulations, as well as HHS OIS and HHS PIM policies and standards, as applicable to the IT System Inventory.
7.9. OpDiv CEA
The OpDiv CEA must:
- Ensure a current and accurate OpDiv IT System Inventory is maintained within the repository, as detailed in Appendix A;
- Collaborate with Business Owners, System Owners, and other functional stewards to ensure accuracy of the IT System Inventory information;
- Ensure IT System information is maintained throughout the lifecycle in compliance with this Policy and in collaboration with the OpDiv CISO; and
- Coordinate with the HHS SAOP in sharing applicable inventory information for analytics and to comply with various reporting requirements.
7.10. OpDiv CISO
The OpDiv CISO must:
- Ensure IT system information is maintained throughout the lifecycle in compliance with this Policy and in collaboration with the OpDiv CEA; and
- Provide coordination and validation of the IT system data used in the OpDiv HHS OIS System Inventory.
7.11. OpDiv Senior Official for Privacy (SOP)
The OpDiv SOP must:
- Collaborate with the OpDiv CEA in sharing Cybersecurity, Privacy and IT System Inventory related information for analytics and to comply with various reporting requirements as detailed in Appendix A.
7.12. OpDiv IT CPIC Officer
The OpDiv IT CPIC Officer must:
- Ensure IT System Inventory information is maintained throughout the IT system lifecycle in compliance with this Policy and in collaboration with the OpDiv CEA;
- Validate and align IT System-to-Investment relationships and ensure it is managed in collaboration with OpDiv CEA.
7.13. Business Owner
The Business Owner is the executive in charge of the organization who serves as the primary customer and advocate for an IT investment. The Business Owner must:
- Ensure the System Owners are registering and maintaining their individual IT System(s) to provide a current and accurate IT System Inventory, as detailed in Appendix A.
7.14. System Owner
The System Owner is the technical manager of an IT System and manages the system under the direction of one or more Business Owners. The System Owner must:
- Collaborate within their OpDiv to register, document, and maintain their individual IT System(s) throughout their lifecycle to provide a current and accurate IT System Inventory, as detailed in Appendix A;
- Provide inventory data to Business Owners for the purpose of registering and maintaining their individual IT System(s) in the IT System Inventory; and
- Share required IT System Inventory information for their individual IT System(s) with the OpDiv CEA, OpDiv CISO, OpDiv SOP, and OpDiv CPIC Officer as specified in Appendix A.
8. Information and Assistance
HHS Office of Enterprise Architecture is responsible for the development and management of this Policy. Questions, comments, suggestions, and requests for information about this Policy should be directed to HHS_EA_Program@hhs.gov.
9. Effective Date and Implementation
The effective date of this Policy is the date on which the policy is approved. This Policy must be reviewed, at a minimum, every three (3) years from the approval date. The HHS CIO has the authority to grant a one (1) year extension of the Policy. To archive this Policy, approval must be granted, in writing, by the HHS CIO.
10. Approval
/S/
Perryn B. Ashmore, Chief Information Officer (CIO) (Acting)
12/15/2020
11. Concurrence
/S/
Scott W. Rowell, Assistant Secretary for Administration (ASA)
12/30/2020
Appendix A: Procedures
Please note that this appendix is subject to change at any time. The current version of this Policy will always reside in the OCIO Policy Library.
IT System Inventory Management Process
The IT System Inventory management process consists of discovery and registration, documentation and maintenance, and decommission. A series of activities for each life cycle stage is described in Figure 1.
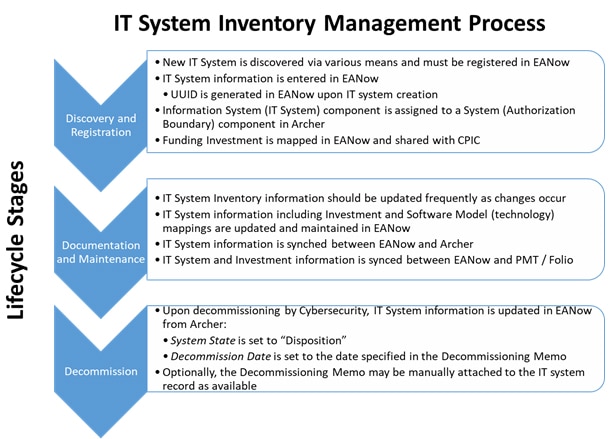
Figure 1 - IT System Inventory Management Process
Discovery and Registration
An IT system is a discrete set of information resources organized for the collection, processing, maintenance, transmission, and dissemination of information, in accordance with defined procedures, owned or operated on behalf of, and automated to support HHS’s or OpDiv’s mission. An IT system is the codification of business requirements, automated to support a specific mission- or business-related function. An IT system typically encompasses the hardware, software, information, data, applications, communications, and the human resources needed to run the IT system. An IT system is funded by one or more investments. An IT system is not a Cybersecurity system authorization boundary or a program.
It is recommended that an IT system is defined to the appropriate level of granularity to ensure transparency into the underlying IT capabilities fulfilling the specific mission- or business-related functions. For example, multiple IT Systems residing on a single platform or aggregated into a single IT system would ideally be represented individually. Greater granularity allows IT systems to be better managed from an enterprise perspective.
From a Cybersecurity perspective, an IT system must be part of a system / authorization boundary.
IT systems may be discovered through various means including but not limited to the following: the HHS Enterprise Performance Life Cycle (EPLC), investment reviews, budget requests, acquisitions, expenditures, network scans, Cybersecurity audits, and system authorization boundary Authority to Operate (ATO) requests and renewals.
An IT system must first be registered in EANow. An IT system is uniquely identified by its Universally Unique Identifier (UUID), which is generated upon its creation in EANow.
Once an IT system has been registered in EANow, it is shared with both HHS OIS and HHS PIM and is assigned to a system boundary as an information system component in Archer.
From a Cybersecurity perspective, a system boundary and all of its other components are to be registered in Archer as detailed in the HHS System Inventory Management Standard.
Documentation and Maintenance
Information in EANow is documented and must be kept up to date throughout the lifecycle of an IT system. The information maintained for an IT system includes but is not limited to, its name, acronym, description, initial operating date, system state, system type, cloud enabled status, funding investment(s) and associated software / technologies.
From a Cybersecurity perspective, information regarding the system boundary and all of its other components are to be documented and maintained in Archer as detailed in the HHS System Inventory Management Standard.
From a CPIC perspective, information regarding the investment is to be documented and maintained in the Portfolio Management Tool (PMT) / Folio.
Decommission
When an IT system is ready to be retired, its decommissioning must be coordinated between EA and Cybersecurity. In EANow, the decommission date of the IT system must be entered to reflect the date of the decommissioning memo. After the decommission date has been updated, the system state of the IT system must be updated to be “Disposition”. Information about a decommissioned system will be retained in EANow for seven (7) years in accordance with the guidance from the National Archives and Records Administration (NARA).
From a Cybersecurity perspective, information regarding the system boundary and its components needs to be updated to reflect the decommissioning of the IT system in Archer as detailed in the HHS System Inventory Management Standard.
IT System Inventory Milestones
Major milestones of the IT System inventory include a Semiannual IT System Inventory Cleanup occurring in July and December before the initial IT Budget and the Passback submissions occurring in September and January as depicted in Figure 2.
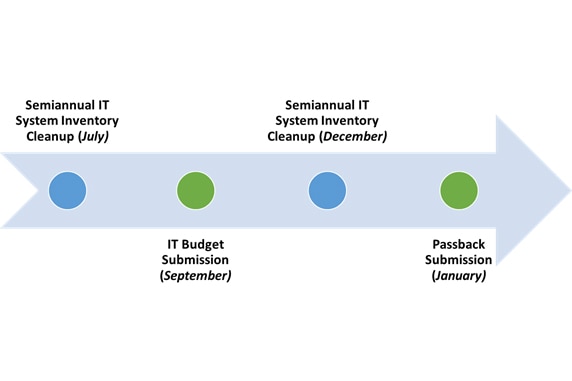
Figure 2 - IT System Inventory Milestones
Semiannual Validation
Performing a semiannual validation helps to ensure that only valid IT systems (including those that have been decommissioned) remain. By confirming that the inventory is both current and accurate, an effective exchange of information between HHS Enterprise Architecture (EA), HHS OIS, and HHS CPIC is possible. Having accurate information across these related data sources makes possible organizational enterprise-wide analysis and data visualization of the Department’s IT assets and supports the Department’s required reporting to Office of the Inspector General (OIG), Department of Homeland Security (DHS), OMB, and Government Accountability Office (GAO).
The following are examples of things that may have been modeled in EANow, but are not valid IT systems, and therefore may be removed from the inventory:
- System Authorization Boundaries, Privacy Impact Assessments (PIA), Common Control Providers (CCP), and Programs
- Placeholders for IT systems that were modeled, but never became operational
- IT systems that have been decommissioned for more than 7 years
OMB IT Budget Submission
The requirements for the OMB IT Budget Submission may change from year to year. In general, the IT system and any supporting software technologies are to be reported along with its funding investment(s) in support of the CPIC IT Portfolio Summary and Passback submissions as detailed in the annual OMB IT Budget Guidance.
Data Sharing
Information is currently shared among HHS EA, HHS OIS, and HHS CPIC using EANow, HSDW / Archer, and PMT / HHS Folio respectively.
HHS EA is the authoritative source for the IT system inventory, which is maintained in EANow. For all data exchanges including IT systems, the UUID is to be used as the primary key.
HHS OIS is the authoritative source for the HHS OIS System Inventory (i.e., the system authorization boundaries), which is maintained in HSDW / Archer. IT system inventory data is included in the HHS OIS System Inventory as all IT systems must be a part of a system authorization boundary.
CPIC is the authoritative source for the IT investment portfolio, which is maintained in PMT / HHS Folio. For all data exchanges including investments, the Unique Investment Identifier (UII) is to be used as the primary key.
Reporting
Relevant information about IT systems is maintained in EANow in order to support various HHS, OMB, and GAO reporting requirements as well as for analytics and analysis.
FISMA
All IT systems in EANow must be part of a system authorization boundary in HSDW / Archer and must be included in the HHS OIS System Inventory to meet the FISMA reporting requirements as detailed in HHS System Inventory Management Standard.
Legacy IT Modernization
All IT systems in EANow must specify supporting component software and technologies (e.g., operating systems, databases, middleware, business applications, business intelligence, software development, and productivity) in order to support Legacy IT Modernization analysis and mitigation of IT systems with end-of-life and obsolete software.
Analytics
Information about all IT systems in EANow will be used to provide meaningful analytics to support IT Budget Reviews, Legacy IT Modernization efforts, technological risk, and alignment to business.
Appendix B: Standards
Please note that this appendix is subject to change at any time. The current version of this Policy will always reside in the OCIO Policy Library.
Minimum Data Requirements
Data Elements
Tables 1-6 provide information on EANow data elements including the cardinality of their relationships (i.e. zero to one [0..1], one to one [1..1], one to many [0..*], many to many [*..*]), which elements are required for any system, edit rights, and authoritative sources for each element. For detailed descriptions for each of the fields and relationships below, please see the latest version of the EANow Data Dictionary.
Table 1- IT System
| Field / Relationship Cardinality | Required | Rights | Authoritative Source |
|---|---|---|---|
| Name | X | Edit | EA |
| Acronym | X | Edit | EA |
| UUID | X | Read-only | EA |
| OpDiv | X | Read-only | EA |
| Segment [0..1] | X | Edit | EA |
| System State | X | Edit2 | OIS |
| System Type | X | Edit | EA |
| Commercial or Government | Edit | EA | |
| Contains PII | Read-only | OIS | |
| Primary BRM [0..1] | Edit | EA | |
| Cloud Enabled | X | Edit | EA |
| Average Number of User Per Month | Edit | EA | |
| Description | X | Edit | EA |
| Initial Operating Date | X | Edit | EA |
| Decommission Date | For decommissioned systems only | Edit3 | OIS |
| Last Major Tech Refresh Date | Edit | EA | |
| Anticipated Major Tech Refresh Date | Edit | EA | |
| System Owner | Edit4 | OIS | |
| Business Owner | Edit5 | OIS | |
| ISSO | Read-only | OIS | |
| Secondary BRM(s) [0..*] | Edit | EA | |
| Uses Software Model(s) [0..*] | X | Edit6 | EA |
| Owning Organization(s) [0..*] | X | Edit | EA |
| Funding Investment(s) [0..*] | X | Edit | EA |
| Parent [0..1] | |||
| Subsystem(s) [0..*] | Edit | EA | |
| SUIC | X | Read-only | EA |
| FIBF Product Function Code(s) [0..*] | Edit | EA | |
| Security Boundary Identifier | Read-only | OIS |
Table 2- Investment
| Field / Relationship | Required | Rights | Authoritative Source |
|---|---|---|---|
| Name | X | Read-only | CPIC |
| Current UII | X | Read-only | CPIC |
| OpDiv | X | Read-only | CPIC |
| Previous UII | Read-only | CPIC | |
| Primary BRM [1..1] | X | Edit | EA |
| Segment [0..1] | Edit | EA | |
| Type | Read-only | CPIC | |
| Description | Read-only | CPIC | |
| Secondary BRM(s) [0..*] | Edit | EA | |
| Funds IT System(s) [0..*] | Edit | EA | |
| Sponsoring Organization(s) [0..*] | Edit | EA |
Table 3 - BRM
| Field / Relationship | Required | Rights | Authoritative Source |
|---|---|---|---|
| Name | Read-only | EA | |
| Code | Read-only | EA | |
| Description | Read-only | EA | |
| Segment [0..1] | Read-only | EA |
Table 4 – Segment
| Field / Relationship | Required | Rights | Authoritative Source |
|---|---|---|---|
| Name | Read-only | EA | |
| Type | Read-only | EA | |
| Description | Read-only | EA | |
| Domain [0..1] | Read-only | EA |
Table 3- Domain
| Field / Relationship | Required | Rights | Authoritative Source |
|---|---|---|---|
| Name | Read-only | EA | |
| Description | Read-only | EA |
Table 4- Organization
| Field / Relationship | Required | Rights | Authoritative Source |
|---|---|---|---|
| Name | Edit | EA | |
| Alias | Edit | EA | |
| OpDiv | Edit | EA | |
| Parent [0..1] | Edit | EA |
FISMA Reporting Requirements
All IT systems in EANow with a system state designation of operations and maintenance (O&M) must be part of a system’s authorization boundary in HSDW / Archer and are to be included in the HHS OIS System Inventory for the FISMA reporting requirements as detailed in HHS System Inventory Management Standard:
- UUID – the UUID of the IT system
- System Name – the name of the IT system
- Acronym – the acronym of the IT system
- Description – the description of the IT system
- Initial Operating Date – the date the IT system became operational
Legacy IT Modernization Reporting Requirements
All IT systems in EANow should document as many supporting technology component software mappings (e.g. OS, databases, etc.) as feasible in order to support Legacy IT Modernization analysis and mitigation of IT systems for end-of-life and obsolete software:
- UUID – the UUID of the IT system
- System Name – the name of the IT system
- Technopedia Release ID – the release ID of the software product model from Technopedia
- Last Tech Refresh Date – the last refresh date of the software (if applicable)
- Next Anticipated Tech Refresh Date – the next anticipated refresh date of the software (if known)
OMB IT Budget Guidance Requirements
Based on the most recent OMB IT Budget – Capital Planning Guidance - PDF, all IT systems are to be reported along with their funding investments and any supporting software products as part of the CPIC budget submission to OMB. Please note that these data requirements are subject to change from year to year.
- Investment
- UII – the Unique Investment Identifier (from PMT)
- Primary BRM – the primary Federal Enterprise Architecture Business Reference Model (BRM) classification code of the primary BRM mapping
- Investment to IT System
- UII – the Unique Investment Identifier (from PMT)
- UUID - the Universally Unique Identifier of the IT system
- SUIC – the System Unique Identifier Code of the IT system (auto-generated in EANow)
- System Name – the name of the IT system
- Initial Operating Year – the year that the IT system became operational
- System Function(s) – the Federal Integrated Business Framework (FIBF) product code mappings (if applicable)
- Was the System Custom Developed? – if the IT system was custom developed entirely within the government and used no purchased products (i.e., COTS, licensing, etc…) then Yes; Otherwise, No
- IT System to Product
- UUID – the UUID of the IT system
- SUIC – the system unique identifier code of the IT system (auto-generated in EANow)
- Release ID – the release ID of the software product (from Technopedia)
- Product Name – the name of the product (i.e. software) (from Technopedia)
- Vendor Name – the name of the software manufacturer (from Technopedia)
- Version Number - the version of the software (from Technopedia)
- Last Tech Refresh Date – the last refresh date of the software (if applicable)
- Next Anticipated Tech Refresh Date – the next anticipated refresh date of the software (if known)
- Product Expected End of Life – the obsolete date of the software (from Technopedia) (if known)
Appendix C: Guidance
Please note that this appendix is subject to change at any time. The current version of this Policy will always reside in the OCIO Policy Library.
This appendix provides additional non-quantifiable requirements to assist with understanding or complying with the policy statements made in Section 6 of the Policy, when specific standards do not apply.
IT System versus System
IT System
An IT system is a discrete set of information resources organized for the collection, processing, maintenance, transmission, and dissemination of information, in accordance with defined procedures, owned or operated on behalf of, and automated to support HHS's or OpDiv's mission. An IT system is the codification of business requirements, automated to support a specific mission- or business-related function. An IT system typically encompasses the hardware, software, information, data, applications, communications, and the human resources needed to run the IT system. An IT system is funded by an investment and is composed of technological components such as hardware and software.
The information maintained in EANow for an IT system includes but is not limited to, its name, acronym, description, initial operating date, system state, system type, funding investment(s) and associated software / technologies.
System
A system is an authorization boundary of which a component may be an IT system.
A system consists of one or more the following components to be maintained in Archer as depicted in Figure 3 below:
- Information Systems (system, subsystem, major/minor application, child, or standalone system)7 .
- Programs (Cybersecurity program, Privacy program). Programs can be used for controls operated by groups of people (e.g., Cybersecurity program, Privacy program). Programs are also inheritance sources8 .
- Common Control Providers (CCPs). A Common Control Provider specifies controls for other information systems (components) to inherit.9
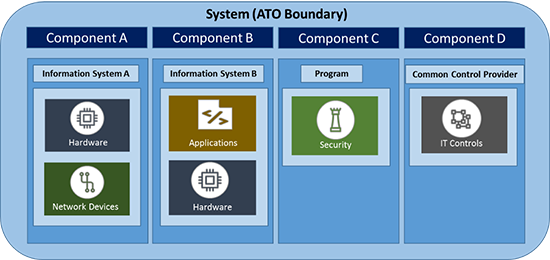
Figure 3 - Archer System and Component Model Diagram
As depicted in Figure 4, EA's construct of an IT system is the same as HHS OIS' construct of an information system component. EANow is the authoritative source for the IT system and its information is synchronized with Archer and is instantiated as an information system component within a system (authorization boundary).
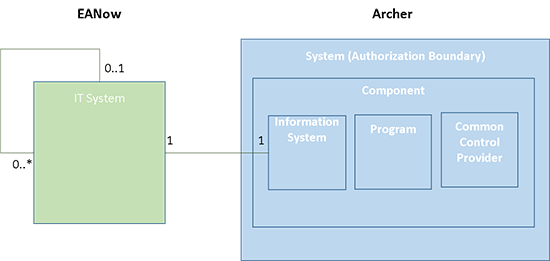
Figure 4 - EANow IT System and Archer System Component Model Diagram
Naming an IT System
The name created to represent the IT system should be descriptive to reflect the purpose or function the IT system is supporting (e.g., Payroll, Grants, Accounting, etc.) and should be approved by the business owners and/or system owners.
The IT system name will be the official name used for all regulatory and compliance reporting requirements related to, but not limited to Enterprise Architecture (EA), Capital Planning (CPIC), Cybersecurity and Privacy, and Records Management throughout its lifecycle.
Although not recommended, the IT system name may be the same as the system authorization boundary name. The system authorization boundary represents aspects extending beyond business systems (security controls, hardware, data exchanges, etc.) as well as the associated business system from EANow.
When developing the name:
- Avoid using an organization name or abbreviation as a prefix or suffix (as the organization may be inferred through the properties and relationships within EANow)
- Avoid using vendor names
- Avoid special characters
Tools
EANow
EANow is an application on the ServiceNow platform and has an extensive set of data sharing capabilities and Application Programming Interfaces (APIs). Information is easily exported from the platform to Excel, CSV, XML, JSON, and PDF from any list view. Representational State Transfer (REST) APIs are available to facilitate more complicated information exchanges.
EANow is the authoritative source for the IT system inventory and is maintained by HHS EA.
HSDW
HHS Security Data Warehouse (HSDW) is an Oracle data warehouse.
HSDW is the authoritative source for the FISMA-related HHS OIS System Inventory and is maintained by the HHS OCIO/OIS Compliance Team. HSDW will be phased out and will be replaced by Archer.
Archer
Archer is an implementation of the Archer Security Governance, Risk Management and Compliance (SGRC) platform.
Archer is the authoritative source for the FISMA-related HHS OIS System Inventory and is maintained by HHS OIS.
PMT
The Portfolio Management Tool (PMT) is an implementation of the Oracle Primavera Portfolio Management platform.
PMT is the authoritative source for the investment portfolio and is maintained by HHS CPIC through the initial FY 2022 IT Budget Submission.
HHS Folio
HHS Folio is an implementation of the GSA Folio platform.
HHS Folio will be the authoritative source for the investment portfolio and is maintained by CPIC starting with the FY 2022 IT Budget Passback Submission.
Appendix D: Forms and Templates
Please note that this appendix is subject to change at any time. The current version of this Policy will always reside in the OCIO Policy Library.
No forms are associated with this Policy.
Appendix E: References
Please note that this appendix is subject to change at any time. The current version of this Policy will always reside in the OCIO Policy Library.
Federal Law
- Clinger-Cohen Act (CCA) of 1996
- E-Government Act of 2002
- Federal Information Security Modernization Act (FISMA) of 2014
- Federal Information Technology Acquisition Reform Act (FITARA) of 2014
- FITARA Enhancement Act of 2017
- Making Electronic Government Accountable by Yielding Tangible Efficiencies (MEGABYTE) Act of 2016
OMB Circulars
- OMB Circular A-11, Preparation, Submission and Execution of the Budget
- OMB Circular A-130, Managing Information as a Strategic Resource
OMB Memoranda
- OMB Memorandum M-15-14, Management and Oversight of Federal Information Technology
- OMB Memorandum M-17-09, Management of Federal High Value Assets
- OMB Memorandum M-19-01, Request for Agency Feedback on the Federal Data Strategy
- OMB Memorandum M-19-21, Transition to Electronic Records
Federal Guidance
- National Institute of Standards and Technology (NIST) Special Publication (SP) 800-37, Guide for Applying the Risk Management Framework to Federal Information Systems: a Security Life Cycle Approach
- NIST SP 800-137, Information Security Continuous Monitoring (ISCM) for Federal Information Systems and Organizations
HHS Policy
- HHS Policy for Capital Planning and Investment Control (CPIC)
- HHS Policy for High Value Assets
- HHS Policy for Information Technology Asset Management (ITAM)
- HHS Policy for Records Management
- HHS Information Security and Privacy Policy (IS2P)
HHS Guidance
- HHS Capital Planning Guide
- HHS Memorandum, FY15 Cybersecurity Information Technology (IT) Priorities
- HHS System Inventory Management Standard
Glossary and Acronyms
In order to provide additional clarity, keyword definitions and any acronyms used in this Policy may be found in alphabetical order in their respective sections below.
Definitions:
- Archer - Archer is the HHS repository managed by OIS for the HHS OIS System Inventory and all related FISMA information for each system authorization boundary
- Authorization Boundary - An authorization boundary is analogous to a System; See System below
- HHS OIS System Inventory - The inventory of all HHS systems and their related FISMA information as maintained by HHS OIS in HSDW / Archer
- EANow - EANow is the HHS-wide repository of enterprise architecture information managed by HHS EA supporting analysis and reporting, serving principally as the Department's authoritative inventory of IT systems
- Folio - Folio is the replacement HHS CPIC repository of the Portfolio Management Tool (PMT); See Portfolio Management Tool below
- HHS Security Data Warehouse (HSDW) - HSDW is the HHS OIS repository for the system inventory (to be replaced by Archer)
- Information System - An information system is a component of a System in Archer; See IT System below
- Information Technology (IT) - "IT" is defined as any services, equipment, or interconnected system(s) or subsystem(s) of equipment, that are used in the automatic acquisition, storage, analysis, evaluation, manipulation, management, movement, control, display, switching, interchange, transmission, or reception of data or information by the agency
- IT Investment -As part of the Budget process, OMB is required to develop and oversee a process for IT budgeting and portfolio management, with a detailed focus on all major capital investments, to include "analyzing, tracking, and evaluating the risks, including information security risks, and results of all major capital investments made by an executive agency for information systems." 40 U.S.C. 11302. OMB also is responsible for IT Portfolio oversight (44 U.S.C. 3602), i.e. the use of information technologies to enhance access of information and delivery of services; and to increase the effectiveness, efficiency, service quality, or transformation of government operations
- IT System - An IT system is a discrete set of information resources organized for the collection, processing, maintenance, transmission, and dissemination of information, in accordance with defined procedures, owned or operated on behalf of, and automated to support HHS's or OpDiv's mission. An IT system is the codification of business requirements, automated to support a specific mission- or business-related function. An IT system typically encompasses the hardware, software, information, data, applications, communications, and people.
- IT System Inventory - The inventory of all HHS IT systems as maintained by HHS Enterprise Architecture in EANow.
- Portfolio Management Tool (PMT) - PMT is the HHS CPIC repository for the IT Budget investment portfolio (to be replaced by Folio)
- Policy - A policy is a set principles, rules, and guidelines formulated or adopted by an organization to reach its long-term goals
- System - A system represents an authorization boundary of which all components to be authorized for operation by an authorizing official and excludes separately authorized systems, to which the system is connected
Acronyms:
- API - Application Programming Interface
- ASA - Assistant Secretary for Administration
- ATO - Authority to Operate
- BO - Business Owner
- BRM - Business Reference Model
- BY - Budget Year
- CCA - Clinger-Cohen Act
- CEA - Chief Enterprise Architect
- CIO - Chief Information Officer
- CISO - Chief Information Security Officer
- COTS - Commercial off-the-shelf
- CPIC - Capital Planning and Investment Control
- CSV - Comma-separated Values
- EA - Enterprise Architecture
- EARB - Enterprise Architecture Review Board
- EPLC - Enterprise Performance Life Cycle
- FEA - Federal Enterprise Architecture
- FIBF - Federal Integrated Business Framework
- FISMA - Federal Information Security Modernization Act
- FITARA - Federal Information Technology Acquisition Reform Act
- FY - Fiscal Year
- GOTS - Government off-the-shelf
- GRC - Governance, Risk Management and Compliance
- HEAR - HHS Enterprise Architecture Repository
- HHS - Department of Health and Human Services
- HSDW - HHS Security Data Warehouse
- HVA - High Value Asset
- IS - Information System
- IS2P - Information Security and Privacy Policy
- ISCM - Information Security Continuous Monitoring
- ISSO - Information System Security Officer
- IT - Information Technology
- JSON - JavaScript Object Notation
- MEGABYTE - Making Electronic Government Accountable by Yielding Tangible Efficiencies
- NARA - National Archives and Records Administration
- NIST - National Institute of Standards and Technology
- OCIO - Office of the Chief Information Officer
- OES - Office of Enterprise Services
- OIS - Office of Information Security
- OMB - Office of Management and Budget
- OpDiv - Operating Division
- PDF - Portable Document Format
- PII - Personally Identifiable Information
- PIM - Privacy and Information Management
- PIV - Personal Identity Verification
- PMT - Portfolio Management Tool
- REST - Representational State Transfer
- SAM - Software Asset Management
- SAOP - Senior Agency Official for Privacy
- SO - System Owner
- SOP - Senior Official for Privacy
- SP - Special Publication
- SUIC - System Unique Identifier Code
- StaffDiv - Staff Division
- SUIC - System Unique Identifier Code
- UII - Unique Investment Identifier
- URL - Uniform Resource Locator
- UUID - Universally Unique Identifier
- VMO - Vendor Management Office
- XML - eXtensible Markup Language
-
1. For HHS OIS, systems are assessed as authorization boundaries for the purpose of granting an Authorization to Operate (ATO). For instructions on managing IT systems in authorization boundaries, refer to HHS System Inventory Management Standard.
- back to note 1 2. Once EANow is integrated with Archer, these fields will be read-only in EANow
- back to note 2 3. Ibid
- back to note 3 4. Ibid
- back to note 4 5. Ibid
- back to note 5 6. Currently, this information is collected manually until an Enterprise-wide Software Asset Management solution is implemented
- back to note 6 7. An Information System component in Archer is the equivalent to an IT system in EANow of which EANow is the authoritative source
- back to note 7 8. A Program component in Archer is a Cybersecurity concept that is not applicable to an IT System in EANow
- back to note 8 9. A Common Control Provider component in Archer is a Cybersecurity concept that is not applicable to an IT System in EANow
- back to note 9

